India's hands on VAPT & Cybersecurity firm
We break in so they can't.
We're not your friendly neighbourhood IT helpdesk. We're the team that rips your systems apart, shows you every crack, and welds them shut — before the real attackers get a chance. VAPT. Digital Intelligence. Risk Advisory. Built in India. Built different.
•
OWASP METHODOLOGY
•
PTES FRAMEWORK
•
ISO 27001 ALIGNED
Web application testing
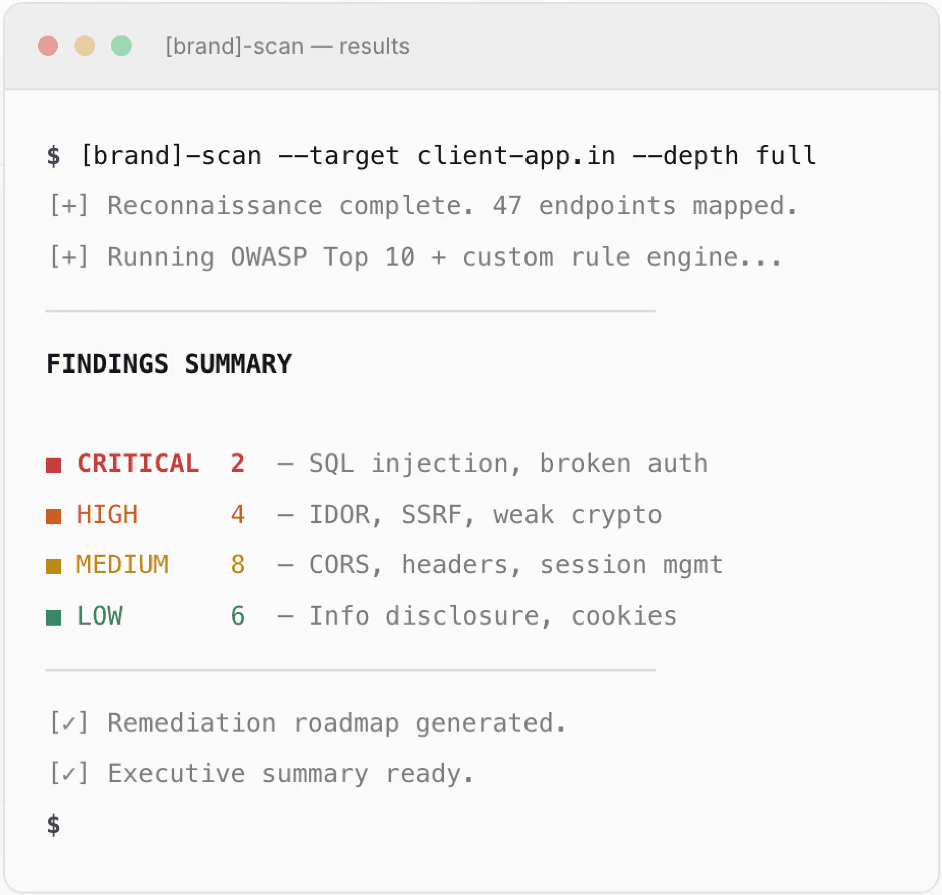
Full OWASP Top 10 coverage plus business logic testing that scanners miss entirely.
Broken Object Level Authorization (BOLA)
Authentication bypass
Business logic flaws
API security testing
Network & infrastructure
We map your perimeter, find lateral paths, and pop shells before the bad guys do.
External perimeter scanning
Internal network assessment
Active Directory attacks
Firewall & segmentation review
Cloud & API security
Misconfigured S3 buckets? Open IAM roles? Unsecured GraphQL? We find it all.
Cloud posture assessment (AWS / Azure / GCP)
IAM & privilege escalation
REST & GraphQL API testing
Container & K8s security
Executive Summary
One-page risk overview for leadership. Zero jargon.
Technical findings
Every vulnerability with severity, PoC, affected endpoints, and remediation.
Remediation roadmap
Findings ranked by risk with ownership, timelines, and effort estimates.
Free re-test
After fixes, we re-test to verify. At no extra charge.
Dark web monitoring
Forums, paste sites, Telegram, marketplaces. If your data leaks, we catch it.
Credential leak detection
Data breach monitoring
Threat actor tracking
Paste site surveillance
Brand protection
Detect phishing domains, fake profiles, rogue apps, and brand impersonation before they reach customers.
Typosquatting detection
Phishing domain takedowns
Fake app identification
Social media impersonation
Threat intelligence
Curated, actionable intelligence on threat actors, TTPs, and campaigns relevant to your industry.
Industry-specific threat briefs
IOC feeds for your SIEM
Attack surface mapping
Executive threat briefings
Compliance & IT audit
Full lifecycle gap analysis, policy drafting, evidence collection, and audit support.
ISO 27001 ISMS implementation
RBI master direction compliance
DPDP Act readiness
SEBI cybersecurity circular
Security governance
Organisational structure, policies, and processes that make security sustainable.
Security policy framework
Risk assessment & treatment
Incident response planning
Board-level security reporting
Security awareness
Phishing simulations and live training that actually change behaviour.
Phishing simulation campaigns
Cyber hygiene training
Executive security briefings
Tabletop exercises
ISO 27001
Full ISMS implementation, internal audits, certification support
RBI
Master direction compliance for banks, NBFCs, payment aggregators
DPDP Act
Data protection assessments, consent frameworks, breach protocols
SEBI
Cybersecurity circular compliance for listed entities, market infra
what clients say
"Their pentest found a critical auth bypass our previous vendor missed for two years. More importantly, they stayed on a call with our devs until it was fixed."
Common questions
Questions. Answers.
What's the difference between a vulnerability scan and a full pentest?
A vulnerability scan runs automated tools and lists known issues. A pentest goes further - our certified testers manually exploit vulnerabilities, chain them together, and test business logic flaws no scanner can catch. We do both, but the manual testing is where real value lives.
How long does a typical VAPT engagement take?
Depends on scope. A single web application typically takes 5–7 business days. Full infrastructure + application test runs 2–3 weeks. You'll get preliminary critical findings within 48 hours.
Will testing break anything in production?
We test carefully. Rules of engagement are agreed upfront, destructive tests avoided in production unless approved, and timing is coordinated with your team. Most clients give us staging first, then we validate critical findings in production under controlled conditions.
What does digital intelligence monitoring involve?
We continuously monitor dark web forums, paste sites, Telegram channels, and the surface web for leaked credentials, exposed databases, brand impersonation, and active threat campaigns. You get real-time alerts and monthly intelligence briefs.
Can findings be used for compliance audits?
Yes. Reports are formatted for ISO 27001, RBI, SEBI, and DPDP audit requirements out of the box. Every finding maps to the relevant compliance control. Many clients use our reports directly in their audit evidence pack.
How quickly can we start?
After a 30-minute scoping call, we send a proposal within 24 hours and can start testing within a week. For urgent deadlines or active incidents, we fast-track to start within 48 hours.
Ready to find out what's actually vulnerable?
30 minutes with a pen tester. Not a sales rep. Not a chatbot. A human who breaks systems for a living.
Where Security Meets Intelligence
